Achieve US Data Privacy Compliance by April 2026: A 4-Step Strategic Guide

The landscape of data privacy is constantly evolving, and businesses operating within the United States are facing an increasingly complex web of regulations. With new laws emerging and existing ones being strengthened, achieving US Data Privacy Compliance is no longer optional but a critical imperative. The looming deadline of April 2026 for several key provisions means that organizations must act decisively and strategically to avoid hefty penalties, reputational damage, and loss of consumer trust. This comprehensive guide outlines a practical, 4-step approach to help your business navigate these challenges and ensure full compliance.
Understanding the intricacies of US data privacy laws can be daunting. Unlike the European Union’s unified General Data Protection Regulation (GDPR), the US operates under a patchwork of state-specific legislation, including the California Consumer Privacy Act (CCPA) and its successor, the California Privacy Rights Act (CPRA), the Virginia Consumer Data Protection Act (VCDPA), the Colorado Privacy Act (CPA), the Utah Consumer Privacy Act (UCPA), and the Connecticut Data Privacy Act (CTDPA), among others. Each of these laws has its unique nuances, definitions, and requirements, making a one-size-fits-all approach challenging. However, by focusing on core principles and adopting a structured methodology, businesses can build a robust framework for US Data Privacy Compliance.
The Urgency of April 2026: Why Now?
While data privacy has been a growing concern for years, the April 2026 timeframe is particularly significant due to the full enforcement of several key amendments and new regulations. This period marks a critical juncture where many organizations will be expected to demonstrate mature and well-established privacy programs. Ignoring these deadlines can lead to severe consequences, including substantial fines, legal challenges, and a significant blow to brand reputation. Consumers are also becoming increasingly aware of their data rights, and non-compliance can quickly erode the trust that is so vital in today’s digital economy. Therefore, proactive planning and execution are paramount for achieving US Data Privacy Compliance.
The Expanding Scope of US Data Privacy Laws
The trend in US data privacy legislation is clear: more states are enacting their own comprehensive privacy laws, and existing laws are being expanded to cover more types of data and processing activities. For example, the CPRA significantly broadened the scope of the CCPA, introducing new consumer rights, establishing the California Privacy Protection Agency (CPPA), and extending the definition of sensitive personal information. Similarly, other state laws have introduced concepts like universal opt-out mechanisms, data protection assessments, and specific requirements for processing sensitive data. This fragmentation necessitates a flexible and adaptable approach to US Data Privacy Compliance.
Step 1: Comprehensive Data Inventory and Mapping
The foundational step in any effective data privacy program is to understand what data your organization collects, where it stores it, how it processes it, and with whom it shares it. Without a clear picture of your data landscape, it’s impossible to assess risks or implement appropriate controls. This process, often referred to as data inventory and mapping, is crucial for achieving US Data Privacy Compliance.
Identify and Catalog All Personal Data
Begin by identifying all systems, applications, and processes that collect, store, or process personal data. This includes customer databases, CRM systems, marketing platforms, HR systems, cloud storage, and even physical documents. For each data point, document:
- Types of Data: What specific categories of personal data are collected (e.g., names, email addresses, IP addresses, health information, biometric data, financial information)? Pay special attention to ‘sensitive personal information’ as defined by various state laws.
- Sources of Data: Where does the data come from (e.g., website forms, third-party vendors, public records, direct input)?
- Purpose of Collection: Why is this data being collected and processed? Is there a legitimate business purpose for each piece of data?
- Location of Storage: Where is the data physically or logically stored (e.g., on-premise servers, cloud providers, third-party data centers)?
- Data Flow: How does the data move within your organization and to external entities? Document all transfers, sharing, and access points.
- Retention Periods: How long is the data kept, and what are the policies governing its deletion or archival?
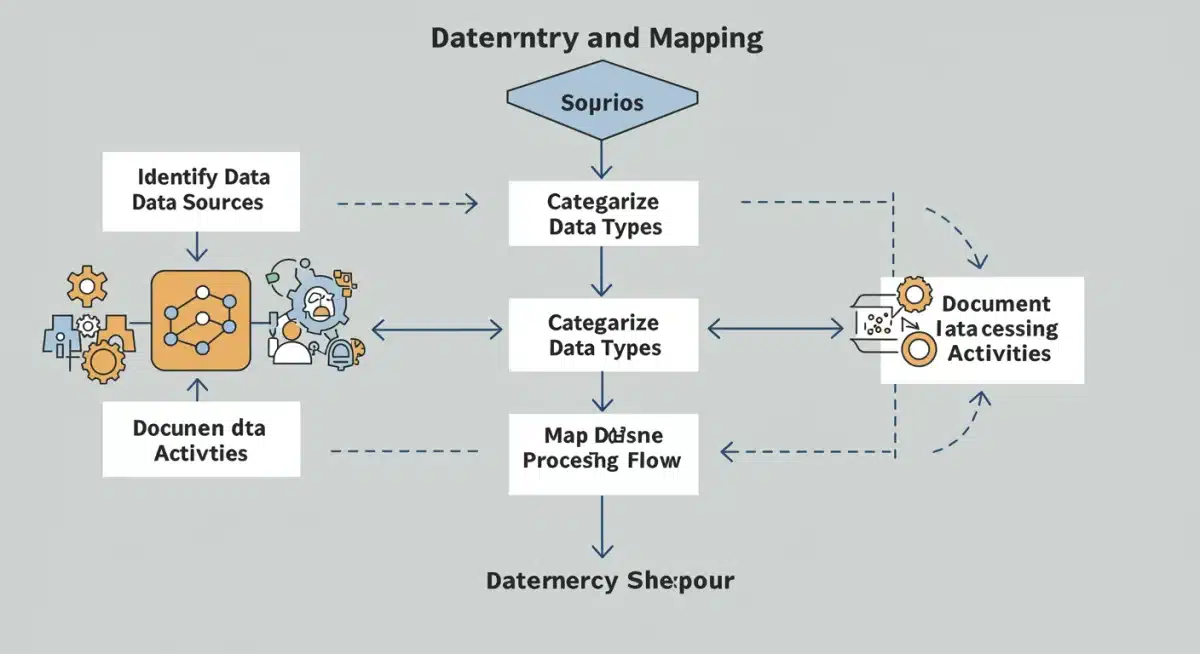
Tools and Techniques for Data Mapping
Manual data mapping can be incredibly time-consuming and prone to error, especially for large organizations. Consider leveraging specialized data discovery and mapping tools that can automate much of this process. These tools can scan your systems, identify personal data, and help visualize data flows. Regular reviews and updates to your data map are essential, as data processing activities can change frequently. This ongoing effort is vital for maintaining US Data Privacy Compliance.
Assess Data Privacy Risks
Once you have a clear understanding of your data landscape, conduct a thorough risk assessment. Identify potential vulnerabilities, such as inadequate security controls, unauthorized access points, or non-compliant data sharing practices. Evaluate the likelihood and impact of data breaches or privacy violations. This assessment will inform your risk mitigation strategies and help prioritize your compliance efforts. Performing Data Protection Impact Assessments (DPIAs) or Privacy Impact Assessments (PIAs) as required by certain state laws is also a key component here.
Step 2: Develop and Implement Robust Privacy Policies and Procedures
With your data inventory complete and risks identified, the next step is to translate this understanding into actionable policies and procedures. This involves crafting clear, legally compliant privacy notices, establishing internal guidelines for data handling, and defining processes for responding to consumer rights requests. A well-defined policy framework is central to demonstrating US Data Privacy Compliance.
Crafting Transparent Privacy Notices
Your public-facing privacy policy must be clear, concise, and easily accessible. It should inform individuals about:
- What personal data is collected.
- The purposes for which the data is processed.
- The categories of third parties with whom data may be shared.
- The rights individuals have regarding their data (e.g., access, deletion, correction, opt-out).
- How individuals can exercise those rights.
- Contact information for privacy inquiries.
Ensure your privacy policy is regularly updated to reflect any changes in data processing activities or legal requirements. Different state laws may require specific disclosures, so tailor your notices accordingly to achieve comprehensive US Data Privacy Compliance.
Establishing Internal Data Handling Procedures
Internal procedures are equally important. These guidelines should dictate how employees handle personal data throughout its lifecycle – from collection to deletion. Key areas to cover include:
- Data Minimization: Only collect data that is necessary for a specific purpose.
- Purpose Limitation: Use data only for the purposes for which it was collected.
- Data Security: Implement appropriate technical and organizational measures to protect data from unauthorized access, loss, or disclosure.
- Employee Training: Regularly train all employees who handle personal data on privacy best practices and your organization’s policies.
- Vendor Management: Establish robust processes for vetting and managing third-party vendors who process personal data on your behalf. Ensure data processing agreements (DPAs) are in place, outlining responsibilities and liabilities.
Operationalizing Consumer Rights Requests
US data privacy laws grant consumers various rights, including the right to access, delete, correct, and opt-out of the sale or sharing of their personal information. Your organization must have clear, efficient, and legally compliant processes in place to handle these requests. This includes:
- Designated Request Channels: Provide multiple, easily accessible methods for consumers to submit requests (e.g., web forms, toll-free numbers, email addresses).
- Verification Procedures: Implement reasonable methods to verify the identity of the person making the request to prevent unauthorized access to data.
- Response Timelines: Adhere to the legally mandated response times for fulfilling requests (e.g., 45 days under CCPA/CPRA, with possible extensions).
- Documentation: Maintain detailed records of all requests received, verification steps taken, and actions performed.
Streamlining these processes is critical for efficient US Data Privacy Compliance.
Step 3: Implement Technology and Security Measures
Policies and procedures are only effective if they are supported by appropriate technological infrastructure and robust security measures. This step focuses on deploying the tools and systems necessary to protect personal data and facilitate compliance. Technology plays a pivotal role in achieving US Data Privacy Compliance.
Data Security Technologies
Protecting personal data from breaches is a cornerstone of privacy compliance. Implement a multi-layered security strategy that includes:
- Encryption: Encrypt data both at rest and in transit.
- Access Controls: Implement strong authentication mechanisms and granular access controls to ensure only authorized personnel can access sensitive data.
- Data Loss Prevention (DLP): Use DLP solutions to prevent sensitive data from leaving your organization’s control.
- Intrusion Detection and Prevention Systems (IDPS): Monitor networks for suspicious activity and respond to threats in real-time.
- Regular Security Audits and Penetration Testing: Proactively identify and address vulnerabilities in your systems.
- Incident Response Plan: Develop and regularly test a comprehensive plan for responding to data breaches, including notification procedures as required by state laws.
Privacy-Enhancing Technologies (PETs)
Beyond basic security, consider adopting PETs that are specifically designed to minimize data exposure and enhance privacy:
- Anonymization and Pseudonymization: Techniques to remove or obscure direct identifiers from data, reducing the risk of re-identification.
- Consent Management Platforms (CMPs): Tools to manage user consent for data collection and processing, especially for website cookies and marketing activities. CMPs are increasingly important for demonstrating US Data Privacy Compliance.
- Data Discovery and Classification Tools: As mentioned in Step 1, these tools help automate the identification and categorization of personal data across your IT environment.
- Privacy Dashboards for Consumers: While not universally mandated, providing consumers with a self-service portal to manage their data preferences and exercise their rights can significantly improve transparency and efficiency.
Leveraging Automation for Compliance
Automation can significantly reduce the burden of compliance tasks. Consider automating:
- Data Subject Access Request (DSAR) Fulfillment: Tools that can help locate, retrieve, and redact personal data in response to consumer requests.
- Consent Preference Management: Automatically apply user consent preferences across all relevant systems.
- Data Retention and Deletion: Implement automated policies for deleting data once its retention period expires.
Step 4: Continuous Monitoring, Auditing, and Adaptation
Data privacy compliance is not a one-time project; it’s an ongoing commitment. The final step involves establishing a framework for continuous monitoring, regular auditing, and adapting your privacy program to new regulations and evolving risks. This iterative process is essential for sustained US Data Privacy Compliance.

Regular Compliance Audits
Conduct internal and, where appropriate, external audits of your privacy program. These audits should:
- Verify that policies and procedures are being followed effectively.
- Assess the effectiveness of technical and organizational security measures.
- Review data processing activities for adherence to legal requirements and internal guidelines.
- Test your incident response plan.
Regular audits help identify gaps and areas for improvement before they lead to compliance violations. This proactive approach is key to maintaining US Data Privacy Compliance.
Stay Abreast of Regulatory Changes
The US data privacy landscape is dynamic. New state laws are constantly being introduced, and existing laws are subject to amendments and new interpretations. Designate a team or individual responsible for monitoring legislative developments and assessing their impact on your organization. Subscribe to legal and industry updates, participate in relevant forums, and consider engaging legal counsel specializing in data privacy.
Ongoing Employee Training and Awareness
Human error remains a leading cause of data breaches. Regular and engaging employee training is crucial. Training should cover:
- The importance of data privacy.
- Specific company policies and procedures related to data handling.
- How to identify and report potential privacy incidents.
- The implications of non-compliance for both the individual and the organization.
Foster a culture of privacy within your organization where every employee understands their role in protecting personal data. This continuous education is vital for ensuring sustained US Data Privacy Compliance.
Review and Update Data Processing Agreements (DPAs)
Regularly review and update your contracts with third-party vendors who process data on your behalf. Ensure that DPAs reflect current legal requirements and adequately protect personal data. Verify that your vendors also adhere to robust privacy and security standards.
Beyond Compliance: Building Trust and Ethical Data Practices
While achieving US Data Privacy Compliance by April 2026 is the immediate goal, forward-thinking organizations understand that privacy is more than just a regulatory checkbox. It’s about building and maintaining trust with customers, employees, and partners. Embracing ethical data practices can differentiate your brand, enhance customer loyalty, and ultimately contribute to long-term business success.
Privacy by Design and Default
Integrate privacy considerations into the design and development of all new products, services, and systems. This ‘Privacy by Design’ approach ensures that privacy is a core component, not an afterthought. Similarly, ‘Privacy by Default’ means that the strictest privacy settings are applied automatically, requiring users to actively opt-in to less private options.
Transparency and User Control
Go beyond the minimum legal requirements by offering greater transparency about your data practices and providing users with intuitive controls over their personal information. This can include personalized privacy dashboards, clear explanations of data usage, and easy-to-use opt-out mechanisms.
Appointing a Privacy Officer (DPO/CPO)
For many organizations, especially those with significant data processing activities, appointing a dedicated Data Protection Officer (DPO) or Chief Privacy Officer (CPO) can be highly beneficial. This individual can oversee the privacy program, ensure compliance, act as a point of contact for regulatory bodies and consumers, and champion privacy within the organization. While not always legally mandated in the US (unlike GDPR), it’s a best practice that reinforces commitment to US Data Privacy Compliance.
Conclusion: A Strategic Imperative for Future Success
The April 2026 deadline for enhanced US Data Privacy Compliance is fast approaching, and businesses cannot afford to delay. By systematically following these four steps – comprehensive data inventory, robust policy development, strategic technology implementation, and continuous monitoring – organizations can not only meet their legal obligations but also build a foundation of trust and ethical data stewardship. Investing in data privacy now is an investment in your company’s future, protecting it from legal risks, enhancing its reputation, and fostering stronger relationships with its stakeholders. Begin your journey today to ensure your business is well-prepared for the evolving data privacy landscape.