Cybersecurity 2026: Proactive Measures for US Digital Resilience

The digital landscape is evolving at an unprecedented pace, bringing with it both immense opportunities and formidable threats. As we look towards 2026, the imperative for robust US Digital Resilience 2026 has never been clearer. Cyberattacks are growing in sophistication, frequency, and impact, targeting everything from critical national infrastructure to individual privacy. Nation-state actors, cybercriminal organizations, and even insider threats pose persistent challenges that demand a proactive and adaptive defense strategy. This article will delve into three pivotal proactive measures that are not just recommendations but urgent necessities for securing the United States’ digital future: advanced threat intelligence, comprehensive zero-trust architectures, and robust supply chain security. These are not merely technical solutions; they represent a fundamental shift in mindset towards anticipating, preventing, and rapidly responding to cyber threats.
The Escalating Threat Landscape: Why Proactivity is Paramount
Before diving into specific measures, it’s crucial to understand the context. The cyber threat landscape of today is characterized by several alarming trends:
- Advanced Persistent Threats (APTs): Sophisticated, long-term attacks often sponsored by nation-states, aiming for espionage, sabotage, or intellectual property theft. These threats are designed to evade detection for extended periods.
- Ransomware as a Service (RaaS): The professionalization of cybercrime has made ransomware more accessible and potent, with devastating consequences for businesses and public services.
- Critical Infrastructure Targeting: Energy grids, water treatment facilities, healthcare systems, and transportation networks are increasingly vulnerable targets, with potential real-world catastrophic impacts.
- Supply Chain Vulnerabilities: Attacks exploiting weaknesses in software or hardware supply chains can compromise thousands of organizations simultaneously, as seen in recent high-profile incidents.
- Geopolitical Tensions: Cyber warfare is now an integral component of geopolitical conflict, with digital attacks preceding or accompanying kinetic actions, making US Digital Resilience 2026 a matter of national security.
Given these realities, a reactive security posture is no longer sufficient. Waiting for an attack to occur before responding is akin to waiting for a house to burn down before calling the fire department. Proactive measures, therefore, are not optional; they are foundational to safeguarding national interests, economic stability, and public trust. The goal for US Digital Resilience 2026 is not just to withstand attacks but to anticipate, deter, and minimize their impact with unparalleled efficiency.
Measure 1: Implementing Advanced Threat Intelligence and Sharing
One of the most critical proactive steps for bolstering US Digital Resilience 2026 is the widespread adoption and effective utilization of advanced threat intelligence. Threat intelligence is not merely a collection of data; it’s analyzed, contextualized information about existing or emerging threats that can be used to make informed decisions about security defenses. For the US, this means moving beyond basic threat feeds to a sophisticated, integrated intelligence ecosystem.
What Constitutes Advanced Threat Intelligence?
- Predictive Analytics: Leveraging AI and machine learning to forecast future attack vectors, methodologies, and targets based on historical data and current trends.
- Human Intelligence (HUMINT): Gathering insights from human sources within cybercriminal or nation-state groups, providing unparalleled visibility into adversary planning.
- Technical Intelligence (TECHINT): Deep analysis of malware samples, exploit kits, and infrastructure used by attackers to understand their capabilities and modus operandi.
- Open-Source Intelligence (OSINT): Monitoring public and semi-public sources, including dark web forums, social media, and academic papers, for indicators of compromise (IOCs) and emerging threats.
- Geopolitical Context: Understanding how global political and economic developments influence cyber threat actors’ motivations and targets.
Strategic Implementation for US Digital Resilience 2026:
- Enhanced Public-Private Partnerships: Establishing seamless, secure, and real-time information-sharing channels between government agencies (e.g., CISA, NSA, FBI) and critical infrastructure operators, technology companies, and private sector cybersecurity firms. This bi-directional flow of intelligence is crucial for a holistic defense.
- Automated Intelligence Integration: Developing frameworks and tools that automatically ingest, correlate, and disseminate threat intelligence into security information and event management (SIEM) systems, security orchestration, automation, and response (SOAR) platforms, and other defensive technologies. This reduces manual effort and accelerates response times.
- Sector-Specific Information Sharing and Analysis Centers (ISACs): Strengthening and expanding ISACs to ensure that industry-specific threats and vulnerabilities are identified and mitigated effectively. These centers serve as vital hubs for sharing actionable intelligence tailored to particular sectors like energy, finance, and healthcare.
- Investment in AI/ML for Threat Analysis: Directing significant research and development funds into AI and machine learning technologies capable of processing vast amounts of threat data, identifying subtle patterns, and generating predictive insights that human analysts might miss.
- International Collaboration: Fostering stronger alliances with international partners to share threat intelligence, coordinate responses, and collectively deter global cyber threats.
The success of advanced threat intelligence hinges on its timeliness, accuracy, and actionability. For US Digital Resilience 2026, the goal is to shift from merely reacting to known threats to proactively identifying and neutralizing potential threats before they can materialize into impactful attacks.

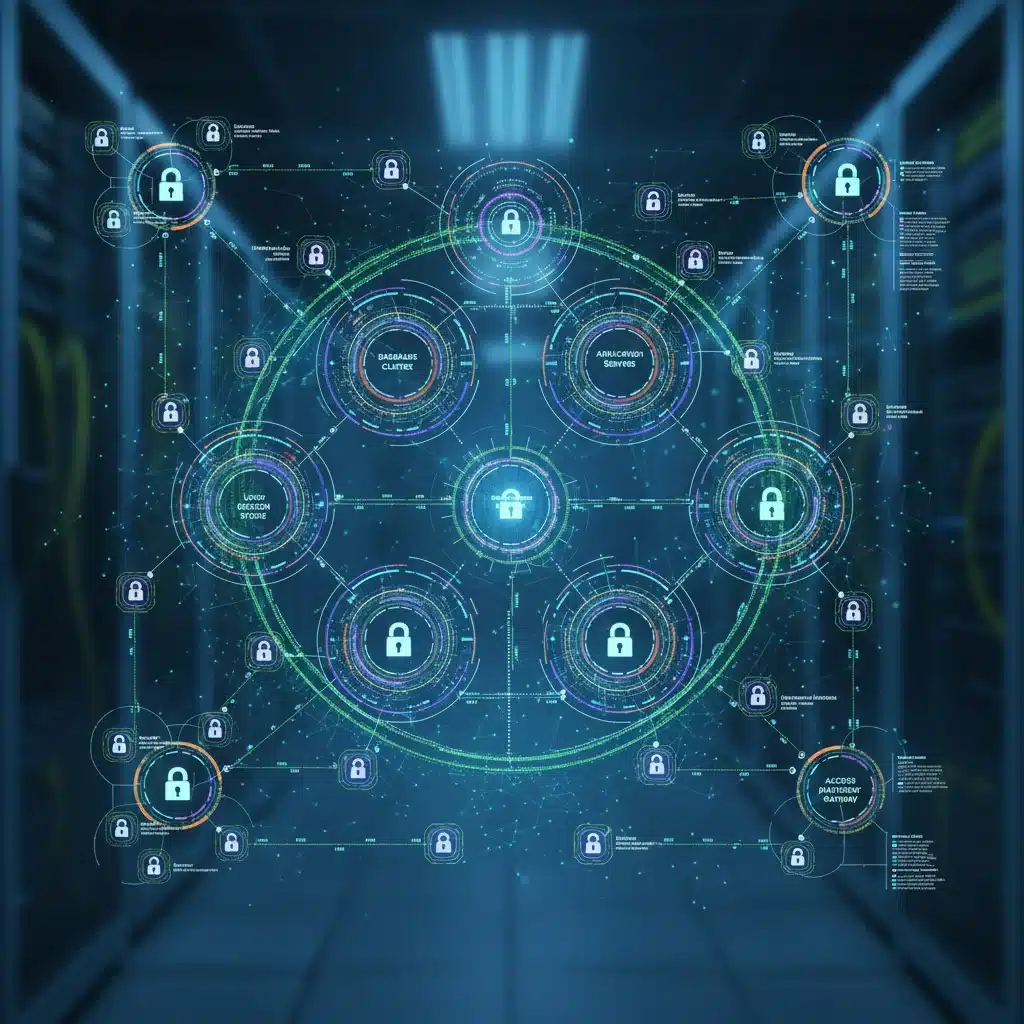
Measure 2: Universal Adoption of Zero-Trust Architectures
The traditional perimeter-based security model, where everything inside the network is implicitly trusted, is fundamentally flawed in today’s interconnected world. It assumes that once an attacker breaches the perimeter, they have free rein. Zero-trust, on the other hand, operates on the principle of ‘never trust, always verify.’ This paradigm shift is essential for achieving robust US Digital Resilience 2026.
Core Principles of Zero Trust:
- Verify Explicitly: All access requests, whether from inside or outside the network, must be authenticated and authorized based on all available data points, including user identity, device health, location, and service being accessed.
- Least Privilege Access: Users and devices should only be granted the minimum access necessary to perform their tasks, and this access should be continuously evaluated.
- Assume Breach: Organizations must operate under the assumption that a breach is inevitable or has already occurred. This leads to designing security layers that limit damage and detect intrusions quickly.
- Micro-segmentation: Networks are divided into small, isolated segments, limiting lateral movement for attackers even if one segment is compromised.
- Continuous Monitoring and Validation: Security posture is continuously monitored, and access privileges are re-evaluated in real-time based on changing risk factors.
Strategic Implementation for US Digital Resilience 2026:
- Government-Wide Mandate and Funding: The US government has already issued executive orders promoting zero trust, but for US Digital Resilience 2026, this needs to translate into broad, funded mandates across all federal agencies and critical infrastructure sectors. This includes providing clear guidelines, reference architectures, and financial support for implementation.
- Identity-Centric Security: Investing in robust identity and access management (IAM) solutions, including multi-factor authentication (MFA) everywhere, privileged access management (PAM), and identity governance. Identity becomes the new security perimeter.
- Device Posture Assessment: Implementing mechanisms to continuously assess the security posture of all devices attempting to access resources, regardless of whether they are corporate-owned or personal. This includes checking for patches, configurations, and malware.
- Network Modernization: Upgrading network infrastructure to support micro-segmentation and software-defined networking (SDN) principles, enabling granular control over traffic flow and access policies.
- Training and Cultural Shift: Educating employees and stakeholders about the importance of zero trust and how it impacts their daily workflows. A successful zero-trust implementation requires a cultural shift towards security-first thinking.
Zero trust is not a single product but a comprehensive security strategy. Its widespread adoption is crucial for protecting sensitive data and critical systems, making it a cornerstone of US Digital Resilience 2026 against sophisticated cyber adversaries.
Measure 3: Fortifying Software and Hardware Supply Chain Security
Recent major cyber incidents have starkly highlighted the profound vulnerabilities within the global supply chain. An attack on one component or vendor can have a cascading effect, compromising numerous organizations downstream. Securing the supply chain is paramount for US Digital Resilience 2026, as it directly impacts the integrity and trustworthiness of the technology infrastructure that underpins everything.
Understanding Supply Chain Risks:
- Software Vulnerabilities: Exploiting weaknesses in open-source libraries, third-party components, or proprietary software introduced during development.
- Hardware Tampering: Malicious modifications to hardware components during manufacturing or transit.
- Insider Threats at Vendors: Compromised or malicious individuals within a vendor organization introducing backdoors or vulnerabilities.
- Sub-component Risks: Lack of visibility into the security practices of sub-tier suppliers, extending the attack surface.
- Lack of Transparency: Difficulty in auditing and verifying the security practices of all entities involved in the supply chain.
Strategic Implementation for US Digital Resilience 2026:
- Software Bill of Materials (SBOMs) Mandate: Requiring all software procured by federal agencies and critical infrastructure to include a comprehensive SBOM. This provides a detailed inventory of all components, libraries, and dependencies, enabling better vulnerability management and risk assessment.
- Enhanced Vendor Risk Management (VRM): Implementing rigorous security assessments, audits, and continuous monitoring programs for all third-party vendors and suppliers. This includes evaluating their cybersecurity posture, incident response capabilities, and adherence to security best practices.
- Secure Software Development Lifecycle (SSDLC): Promoting and enforcing secure coding practices, regular security testing (e.g., static and dynamic analysis, penetration testing), and vulnerability management throughout the entire software development lifecycle, extending to vendor partners.
- Hardware Assurance and Authentication: Developing and deploying technologies for hardware authentication and integrity verification to detect tampering. This could involve cryptographic methods embedded in chips or secure boot processes.
- Supply Chain Mapping and Criticality Assessment: Identifying and mapping critical components and suppliers within the national digital infrastructure. Prioritizing security efforts based on the potential impact of a compromise from specific links in the supply chain.
- Incentivizing Secure Practices: Offering incentives, grants, or preferential treatment to vendors who demonstrate superior cybersecurity practices and transparency, thereby raising the overall security bar across the industry.
Securing the supply chain is a complex, multi-faceted challenge that requires collaboration across industries and government. By focusing on transparency, accountability, and verification, the US can significantly reduce its exposure to these insidious attacks, ensuring the integrity of its digital ecosystem for US Digital Resilience 2026.
Integrating These Measures for Holistic US Digital Resilience 2026
While each of these three measures – advanced threat intelligence, zero-trust architectures, and supply chain security – is powerful on its own, their true strength lies in their synergistic integration. For US Digital Resilience 2026, these are not independent initiatives but interlocking components of a comprehensive national cybersecurity strategy.
- Threat Intelligence informs Zero Trust: Advanced threat intelligence can provide real-time context to zero-trust policies, allowing for dynamic adjustments to access controls based on emerging threats or adversary tactics. For instance, if intelligence indicates a specific IP range is associated with an active campaign, zero-trust policies can immediately restrict access from that range.
- Zero Trust enhances Supply Chain Security: By applying zero-trust principles to vendor access and third-party integrations, organizations can minimize the blast radius if a supply chain component is compromised. Even if a malicious component is introduced, its ability to move laterally or exfiltrate data would be severely limited by granular access controls.
- Supply Chain Security strengthens Threat Intelligence: Secure supply chains mean more trustworthy data sources for threat intelligence. Furthermore, SBOMs and vendor security assessments can provide valuable insights into potential vulnerabilities that adversaries might target, feeding into predictive intelligence efforts.
This interconnected approach creates a resilient, multi-layered defense that is greater than the sum of its parts. It allows the US to not only prevent known attacks but also to adapt rapidly to novel threats and mitigate the impact of successful breaches more effectively.
Challenges and the Path Forward
Implementing these measures on a national scale is not without its challenges. These include:
- Talent Gap: A persistent shortage of skilled cybersecurity professionals to design, implement, and manage these complex systems.
- Legacy Systems: The difficulty and cost associated with modernizing outdated IT infrastructure across various sectors.
- Funding: Securing adequate and sustained funding for research, development, and deployment of advanced security technologies.
- Organizational Inertia: Overcoming resistance to change and fostering a culture of cybersecurity awareness and responsibility.
- Global Nature of Threats: The inherent difficulty in controlling threats that originate beyond national borders.
Despite these hurdles, the urgency of the situation demands immediate and sustained action. The path forward for US Digital Resilience 2026 involves:
- Aggressive Workforce Development: Investing in cybersecurity education, training, and certification programs from K-12 through higher education and professional development.
- Strategic Partnerships: Continuing to foster strong collaboration between government, industry, academia, and international allies.
- Policy and Regulatory Frameworks: Developing clear, enforceable policies and regulations that mandate minimum security standards and encourage best practices across all critical sectors.
- Innovation and Research: Continuously investing in cutting-edge cybersecurity research to stay ahead of evolving threats.
- Continuous Assessment and Adaptation: Regularly evaluating the effectiveness of implemented measures and adapting strategies based on the evolving threat landscape and technological advancements.
Conclusion
The year 2026 is not far off, and the window for establishing comprehensive US Digital Resilience 2026 is rapidly closing. The measures outlined – advanced threat intelligence, universal zero-trust architectures, and robust supply chain security – are not merely theoretical concepts; they are practical, time-sensitive imperatives. By embracing these proactive strategies, the United States can build a formidable digital defense capable of protecting its critical infrastructure, safeguarding its economy, and preserving national security in an increasingly volatile cyber world. The future of digital resilience depends on decisive action today.





